HPKE is scheme provides a variant of public-key encryption of arbitrary-sized plaintexts for a recipient public key. It includes three authenticated variants, including one which authenticates possession of a pre-shared key, and two optional ones which authenticate possession of a KEM private key. HPKE works for any combination of an asymmetric key encapsulation mechanism (KEM), key derivation function (KDF), and authenticated encryption with additional data (AEAD) encryption function. Some authenticated variants may not be supported by all KEMs. We provide instantiations of the scheme using widely used and efficient primitives, such as Elliptic Curve Diffie-Hellman key agreement, HKDF, and SHA2.
Cryspen provides ready to use high assurance implementations of HPKE in Rust as well as services to help integrate HPKE into products.
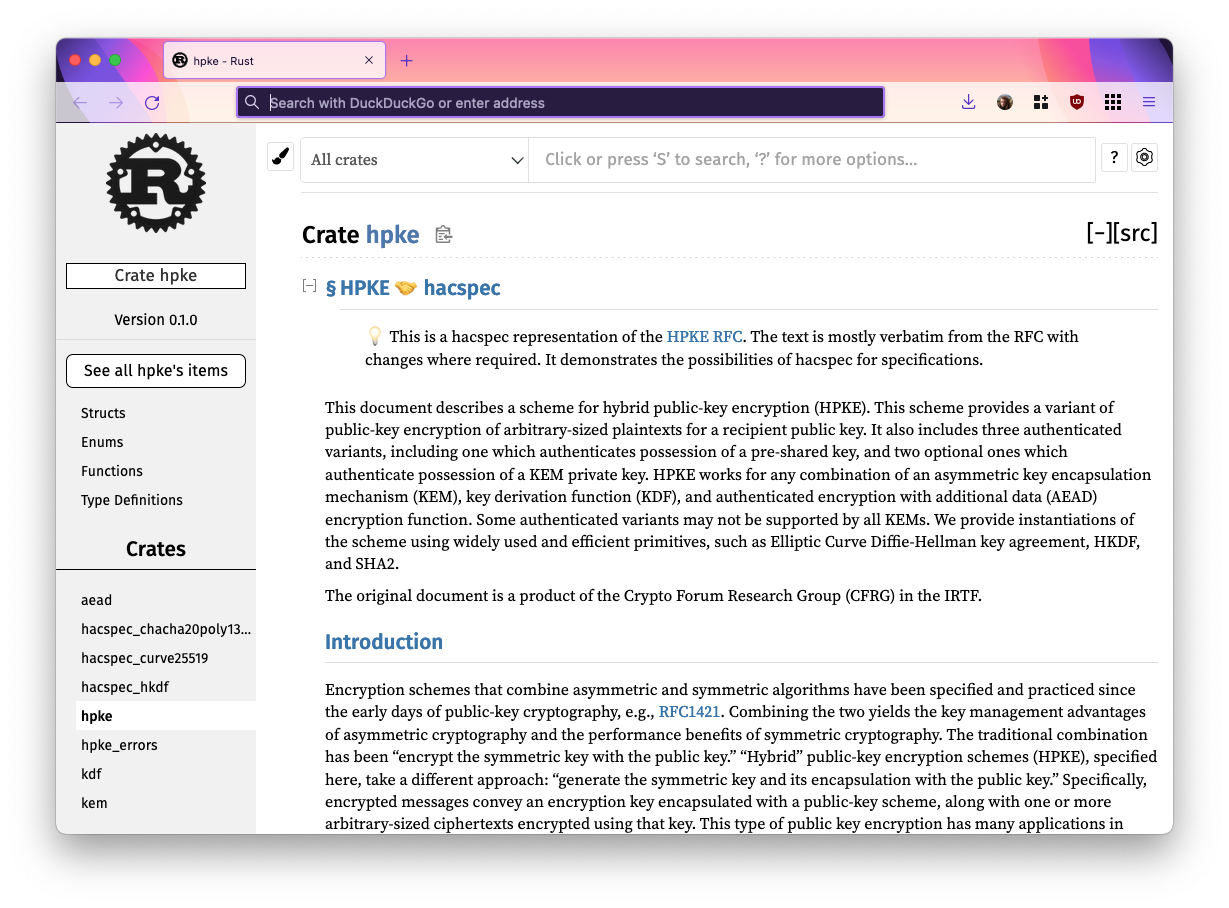
RFC 9180 Annotated Specification Get in touch
Demo
- First generate a key pair for the receiver.
- Then populate the info, additional data, and payload fields on the sender side.
- When clicking the “HPKE Seal” button on the sender the following happens
- The sender retrieves the public key from the receiver that has been generated in the first step.
- The sender uses HPKE to encrypt the payload together with the info and additional data to the receiver’s public key.
- The result is written into the Encoded Shared Secret and Ciphertext fields.
- When clicking “HPKE Open” the receiver uses the private key to retrieve the shared secret and decrypt the ciphertext. The “Info” and “Additional Data” are the same as entered on the sender’s side.